The Democratic Party had its emails hacked, allegedly by Russian agents. Republican Presidential Nominee Donald Trump added fuel to the fire by encouraging the Russians to hack Hillary Clinton’s emails. John Iannarelli, a retired FBI special agent and former head of FBI cyber investigations in Arizona, will discuss cybersecurity.
TED SIMONS: Coming up next on Arizona Horizon--we'll talk about cybersecurity in light of the recent hacks of the Democratic Party emails, and we'll hear about the use of forest biomass to help fuel power stations. Those stories next on Arizona Horizon.
ANNOUNCER: Arizona Horizon is made possible by contributions from the friends of Arizona PBS, members of your PBS station. Thank you!
TED: Good evening and welcome to Arizona Horizon, I'm Ted Simons. The Democratic National Convention continues in Philadelphia with increasing signs that those supporting Bernie Sanders are ready to get behind the official nominee, Hillary Clinton. That's how former Phoenix mayor and State Attorney General Terry Goddard sees it, both in and out of the convention hall.
TERRY GODDARD: I spent a fair amount of time trying to find the gate to get into this convention; I ended up talking to and walking through a lot of the Bernie demonstrators that are still hardcore. They're very disappointed with the results of the primaries, and they want to keep fighting. I encourage them on that. I think this convention has done a lot to encourage them, just to say "Be a part of the process. Be there and make sure that your message and your voice is heard."
Raul Grijalva is certainly the best expresser of that: A strong Bernie supporter--and I think the first in Congress to support Senator Sanders--and through our delegation and the progressive caucus, he was saying, "Look, this is an important cause, the cause goes on." The passions that have been aroused throughout the country and in Arizona certainly, go on because people who were never involved in the process now are. Their voice has been heard.
TED: Programming note: tomorrow night at 10:00, we'll have post-convention analysis in-studio and live from Philadelphia right here on Arizona Horizon.
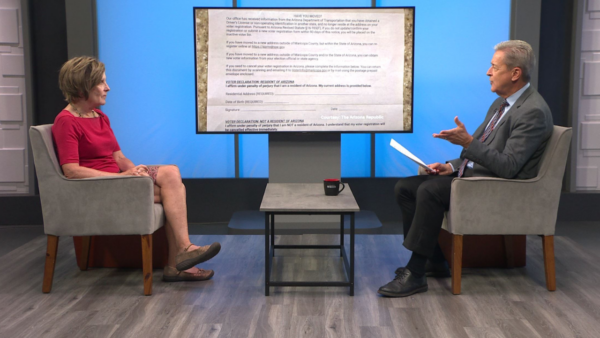
Republican presidential candidate Donald Trump is taking headlines away from the Democratic Convention this week by appearing to ask Russian intelligence agencies to hack democrat Hillary Clinton's emails, in order to find 30,000 messages missing from a personal server that Clinton used to conduct official business as Secretary of State. Joining us now to help put some perspective on all this is John Iannarelli, a retired FBI special agent and former head of FBI cyber investigations in Arizona.
Good to have you here. What exactly happened to these Democratic Party emails?
JOHN IANNARELLI: Well it looks like some entity--it might have been a rouge state, it could have been a private hacker--but someone got in, ahold of these emails sent out over a period of time, and now they're sharing them for the purpose that appears to be to embarrass the Democratic Party.
TED: How do you hack something like this?
JOHN: Not very difficult to do at all. Anything that we have these days, whether it's encrypted or not, there's software out there that you can hack into computer systems. I may not necessarily go into your computer but maybe the server, the service you're getting your email from and look at the information from there. Democratic Party is pretty easy, because it's going to be marked Democratic Party.
TED: If I'm a hacker, what kind of information do I need if I want to hack X, Y, and Z?
JOHN: If you want to hack into an particular person's account, really nothing more than a little social engineering. Maybe I'm gonna go to your LinkedIn and get information as so to help me decide how I'm going to target the account. People aren't very complex when they put passwords together, and that's the real danger.
More times than not, it's that simple. Other times, it's malware like in the Sony hack. People think it was this really convoluted difficult thing from North Korea… it was nothing more than a scam. Somebody clicked on a link, the next thing, you know, North Korea got into that email.
TED: We know someone has done this, how difficult is it to track down who did it?
JOHN: Well, the FBI, which is the primary agency that deals with these type of hacks--they're very good. They've got some really sharp people who work computer crimes. The problem is even if you track them down, are they in a country that we have reciprocity with? We can't convict them over here in the United States unless we bring them back here, which means we'd need to get that country to cooperate.
TED: You're talking about countries here; how often do countries hack into other countries?
JOHN: Well, the individual hackers may be in another country, but frequently we see foreign countries, both our enemies and our friends. There's a lot of spying that goes on in the world and it's not uncommon that even a friendly country will be probing our systems to see what's out there and what they can find.
TED: If you catch France hacking into American government systems or something along these lines, what do they say? What's done diplomatically? That seems like kind of an embarrassing situation.
JOHN: Well, it can be, and that's why the government's State Department gets involved. All sorts of communication go back and forth, but in the world of politics, a lot that have is how the world operates. The real dangers are countries like Iran and North Korea and those who want to do us harm that are hacking into our systems. That's what we have to protect against.
TED: What about Russia? Is Russia a big player when it comes to hacking?
JOHN: Russia and the former Russian mob that has now moved out of violence and more into cybercrime. There's a ton of money to be made, and it's easier to rob a bank with a computer than with a gun.
TED: Would it surprise you if, A: they found out this was Russian influenced and, B: they found out that it was Russian mob influenced?
JOHN: it would not surprise me at all. But just as likely, it might very well be China or any other country that's out there, because we're hacked and attempted hacked by all such countries.
TED: How often do we hack other countries?
JOHN: Realistically, the U.S. government has policies against doing those sort of things, and from the FBI side, there would be serious punishment for anybody engaged. But there are private hackers, private citizens that do this all the time.
TED: I seem to remember the US and maybe Israel hacking into Iran's nuclear program to kind of throw the whole thing haywire a while back. So this thing does happen. It sounds like it's one cyber spy thing happening out there.
JOHN: That's where the wars are going to be fought in the future. It's very easy to get out and get a gun, but how much damage can you really do? Now here in Arizona, if I'm going to shut down the electricity during the summer, where you don't have air conditioning, access to gasoline, your banking accounts… that can do some real damage, and that's what these foreign countries, our adversaries, are trying to do.
TED: So, they're trying to do this. Are we up to speed in terms of cybersecurity?
JOHN: There's always room for improvement. We have some very talented people doing this, but technology changes so quickly, so exponentially that as soon as we find one answer, there's another problem.
TED: I was going to ask about this. I mean, if you work on a case, it seems to me by the time you get done working on the case, the method of hacking and technology could have changed exponentially.
JOHN: Absolutely. What the FBI is always doing is bringing on fresh talent: young recruits who are fresh out of the cyber scene, out of college with their degrees, who we can throw at these sorts of problems. And we also contract out a lot of the big companies that are the 10-gallon brains in the cyber world that we can have them look at malware and look at computer code, so the agents with guns can go out on the street and do the job.
TED: Is that at tough sell? I mean, we all know what kind of salaries these young people can make at Silicon Valley and elsewhere. That seems like that's pretty rough.
JOHN: Well, I'll tell you that no one joins the FBI for the money or the federal government in general. They join the FBI because it's a job unlike anything else where you're going to see things that people will never get an opportunity to see. A lot of the people, who come to us, forgo those big salaries because they know they have a front row seat to the world that nobody else is ever going to have.
TED: You mentioned in the past that the next wars will be very much cyber-oriented. Are we prepared for that? I mentioned whether or not we have cyber security, that's one thing, but are we prepared in case all of these systems shut down? The cloud goes away, if you will?
JOHN: I believe we are. The FBI has a private partnership with the public sector referred to as InfraGard. All different entities involving critical infrastructure they need on a regular basis. Here in Arizona, we have nearly 2,000 members of InfraGard from all over the state, where we get together and we discuss the issues. We share what we see, and likewise, we prepare to keep ourselves safe.
TED: Before you go, Donald Trump is saying he hopes Russia will do another hack and release Clinton's emails, and hopes that Russia penetrates U.S. servers. Some are saying this is tantamount to treason. Is it tantamount at least to a threat to U.S. security?
JOHN: Well as a former FBI agent and attorney, I can tell you it doesn't even come close to the elements of a crime, but considering both the Democrats and Republicans have enough issues when it comes to emails these days, I suggest it's a subject they should probably just stay away from throwing stones at.
TED: He wants whoever is hacking to give this information to the FBI. If the FBI received information from people illegally hacking into American corporations, organizations, whatever, what does the FBI do?
JOHN: We take that information, work with it and try to track down who is doing what for what. That happens all the time, people with information and sources, come to the FBI and that's how we catch some of these hackers.
TED: So the information wouldn't be pooh-pooh, just because it came from a hacker doing something illegally?
JOHN: No, actually hackers doing things illegally or any criminals doing something illegally, that is the way law enforcement gets information.
TED: Very good. Great information, good to have you here.
JOHN: Thank you for your time.
----------
ANNOUNCER: Get the inside scoop on what's happening at Arizona PBS! Become an insider. You'll receive weekly updates on the most anticipated upcoming programs and events. Get the Insider delivered to your email inbox. Visit azpbs.org to sign up today.
----------
John Iannarelli: A retired FBI special agent and former head of FBI Cyber Investigations in Arizona